If you’re running a fast-growing business in 2026, payment security isn’t just a checkbox—it’s your safety net. As the digital world changes rapidly, you need to understand how to protect your customers (and, let’s be honest, your peace of mind) every time money changes hands online.
In FY2022-23, banks reported a total number of 6,659 cases of digital payment fraud. According to the IBM Security report of 2023, the average cost of a data breach in India reached INR 17.9 crores. This represents a 28% increase since 2020! That’s why you must prioritise payment security to protect your funds and ensure customer loyalty.
You’re probably wondering what makes a payment gateway truly secure. In this article, we’ll explore payment security fundamentals, dive into various protection methods, and share practical strategies to safeguard your business and customers.
Table of Contents
Key takeaways
- Payment security protects sensitive financial data through encryption, tokenisation, and multi-factor authentication
- PCI DSS compliance is mandatory for businesses processing card payments, with specific requirements based on transaction volume
- Common threats include phishing, data theft, and payment fraud—requiring proactive detection and prevention strategies
- A comprehensive security strategy includes risk assessment, employee training, and continuous monitoring
- Choosing the right payment partner with advanced security features is crucial for business protection
What is Payment Security?
Payment security refers to the comprehensive set of processes, techniques, and protocols you use to safeguard online and offline financial transactions, protecting sensitive payment and personal information from threats like fraud, unauthorised access, and privacy breaches.
Think of payment security as multiple layers of protection working together—like having several locks on your front door. You can choose to apply these layers depending on your business requirements and risk tolerance. Some of the most commonly used payment security layers are:
- Encryption
- Tokenization
- Authentication
Principles of Payment Security
The foundation of effective payment security rests on four core principles that guide every security decision you make. These principles ensure your payment systems remain robust against evolving threats whilst maintaining smooth user experiences.
Confidentiality
Confidentiality ensures that sensitive payment information remains accessible only to authorised parties. This means encrypting cardholder data during transmission and storage, implementing strict access controls, and ensuring that payment details never appear in plain text where unauthorised individuals could access them.
Integrity
Integrity guarantees that payment data remains accurate and unaltered throughout the transaction process. This involves using cryptographic hashes, digital signatures, and checksums to detect any unauthorised modifications to payment information during processing or storage.
Availability
Availability ensures that your payment systems remain operational and accessible when customers need them. This includes implementing redundant systems, regular backups, and robust infrastructure that can withstand both technical failures and cyber attacks without disrupting payment processing.
Authenticity
Authenticity verifies that all parties in a payment transaction are who they claim to be. This involves implementing strong authentication mechanisms, digital certificates, and verification processes that confirm the identity of customers, merchants, and payment processors before processing transactions.
Types of Payment Security
Payment security encompasses various measures to protect sensitive financial information during transactions. Understanding these different types helps you build a comprehensive defence strategy for your business.
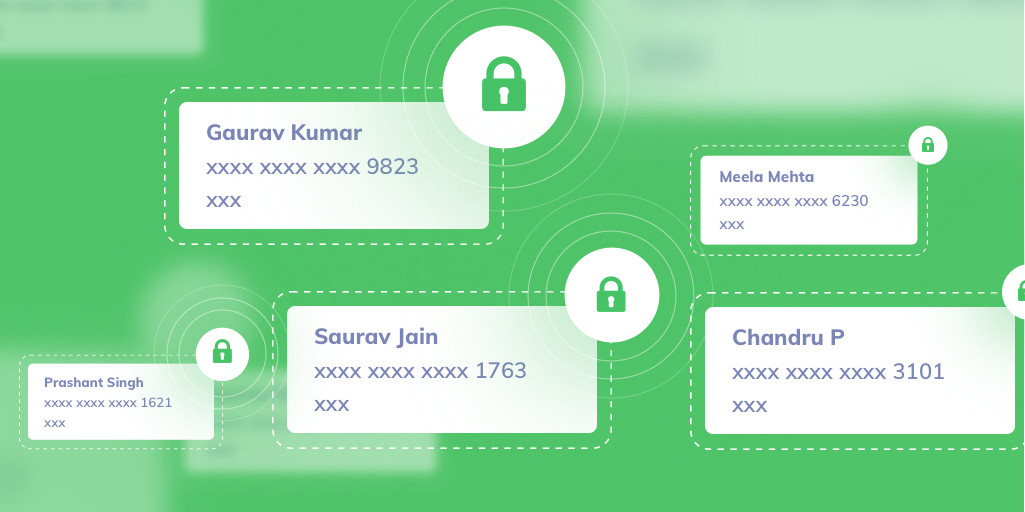
1. Tokenization
Tokenization replaces sensitive data, such as credit card numbers, with unique tokens. This token is meaningless to unauthorised users, thus preventing the risk of data breach.
Payment data is collected, tokenized, securely stored, and then used for transactions. Most payment gateways employ tokenization for enhanced security.
Related Read: What is Card Tokenization?
2. Encryption
Encryption converts data into a coded format, decipherable only via the correct key. The two types of encryption are symmetric (the same key for encryption and decryption) and asymmetric (a pair of public and private keys).
Widely used encryption protocols like SSL (Secure Socket Layer) and TLS (Transport Layer Security) help establish secure connections during online transactions. You should prioritise using the latest encryption protocols and update them regularly. You should also store and manage encryption keys securely to prevent them from falling into the wrong hands.
3. Authentication
Authentication verifies user identity before processing payments. You can activate different authentication modes for users to access your platform, each offering varying levels of security. These include –
Single-factor authentication
Requires one verification method (e.g., a password)
Two-factor authentication
Involves two different verification methods to enhance security (e.g., a password followed by a security question)
Multi-factor authentication
Incorporates additional verification factors, like biometrics or one-time passwords (OTPs).
Types of authentication methods
One-time passwords (OTPs)
These are temporary, single-use codes. Businesses usually send OTPs via phone number or email ID to verify user identity.
Biometrics
It involves the use of unique physical or behavioural characteristics of an individual to verify their identity. This can include a fingerprint scan or facial recognition.
CVV (Card Verification Value)
Card Verification Value is a 3-4 digit code present on debit and credit cards. It verifies that the user physically possesses the card since the code is not embedded into the magnetic chip or stripe. This reduces the risk of fraud during online or card-not-present transactions.
Address Verification Service (AVS)
AVS matches the provided delivery address with the cardholder’s billing address.
The benefits of this method include –
- Fraud prevention: It prevents fraudulent transactions by confirming the address.
- Cost savings: It reduces costs related to chargebacks, shipping errors and customer service.
- Compliance: It helps your business meet legal requirements for identity verification.
- Efficient shipping: AVS ensures on-time deliveries and reduces the chances of returns.
However, there are some shortcomings to this authentication mode as well
- Limited accuracy: AVS relies on exact matches between the provided address and the billing address. This can lead to false rejections for minor discrepancies, such as abbreviations or typos.
- Address privacy concerns: It raises privacy concerns as it involves sharing personal address information. Some users may be uncomfortable with this.
- Doesn’t prevent the use of stolen cards: AVS is not designed to prevent transactions using stolen cards if the thief has access to the billing address information.
Related Read: What Is Address Verification Service (AVS) and How Does It Work?
3D Secure
3D Secure is an online payment security protocol for credit and debit card transactions. It requires cardholders to provide a unique authentication code, such as an OTP, for online purchases. This helps verify user identity and mitigate fraud.
It involves three domains of payer authentication:
- Acquiring domain (merchant): The online retailer or merchant where the purchase is being made.
- Issuing domain (bank): The bank that issued the credit / debit card.
- Interoperability domain (3D Secure protocol): The intermediary that facilitates secure communication and authentication between the two aforementioned domains.
The latest version, 3D Secure 2 (3DS2), is an enhanced version of the 3D Secure protocol. It provides a more secure and seamless experience during online transactions. 3DS2 supports a wider range of authentication methods, making it more adaptable to the evolving landscape of online payments. In addition to OTPs and biometric verification, 3DS2 also makes use of the following methods –
- Device fingerprinting: It analyses the unique characteristics of the cardholder’s device (the device’s IP address, location and browser type) to verify their identity.
- Risk-based authentication (RBA): This method assesses the risk level of a transaction based on factors such as location and transaction amount. If the transaction is considered low risk, it may not require additional verification.
- Password authentication: Cardholders need to enter a password to authenticate their identity. It may be the same password that they use for online banking.
- Out-of-band authentication: This verifies a transaction via a different channel, such as a phone call to the cardholder.
Explore Razorpay’s Payment Solutions
Common Payment Security Risks and Threats
Understanding the threats your business faces is the first step in building effective defences. Payment security risks have evolved dramatically, with cybercriminals using increasingly sophisticated methods to exploit vulnerabilities in payment systems.
Did You Know?
<i\>Phishing attack volume has skyrocketed by 4,151% since the launch of ChatGPT in November 2022. According to the 79 percent of organizations experienced payments fraud attacks or attempted fraud in 2024, with Business Email Compromise cited as the number one avenue for fraud attempts by 63 percent of respondents surveyed.</i\>
Phishing and Social Engineering Attacks
Phishing attacks trick users into revealing sensitive information through fraudulent emails, websites, or messages that appear legitimate. These attacks have become more sophisticated, often targeting specific individuals within organisations (spear phishing) or impersonating trusted brands and services.
Payment Card Fraud
Card fraud occurs when criminals use stolen or counterfeit payment cards to make unauthorised purchases. This includes card-not-present fraud for online transactions, where fraudsters use stolen card details without physically possessing the card.
Account Takeover Attacks
Cybercriminals gain unauthorised access to customer accounts by stealing login credentials through data breaches, phishing, or credential stuffing attacks. Once inside, they can modify payment methods, make fraudulent purchases, or steal stored payment information.
Third-Party Vulnerabilities
Your payment security is only as strong as your weakest link. Third-party payment processors, plugins, or integrations can introduce vulnerabilities that criminals exploit to access your payment systems or customer data.
Insider Threats
Malicious or negligent employees with access to payment systems can pose significant risks. This includes intentional data theft, selling customer information, or accidentally exposing sensitive data through poor security practices.
Man-in-the-Middle Attacks
These attacks intercept communications between customers and payment systems, allowing criminals to steal payment information or modify transaction details. They’re particularly common on unsecured public Wi-Fi networks.
Fraud Detection and Prevention Techniques
Modern fraud prevention goes beyond basic security measures. You need sophisticated detection systems that can identify suspicious patterns and stop fraudulent transactions before they complete, whilst ensuring legitimate customers aren’t inconvenienced.
According to recent research from Feedzai, the AI fraud detection market is poised to grow to $39.1 billion by 2030, reflecting the industry’s recognition of AI’s critical importance in combating increasingly sophisticated fraud.
Machine Learning and AI-Driven Detection
Machine learning algorithms analyse vast amounts of transaction data to identify patterns that indicate fraudulent activity. These systems continuously learn from new data, adapting to emerging fraud techniques and reducing false positives over time.
Risk Scoring and Velocity Checks
Risk scoring assigns a numerical value to each transaction based on various factors such as transaction amount, location, time of day, and customer behaviour patterns. Velocity checks monitor the frequency and volume of transactions from specific accounts or payment methods to detect unusual activity.
Device Fingerprinting
This technique creates a unique identifier for each device accessing your payment system by analysing characteristics such as browser type, screen resolution, installed plugins, and network configuration. Unusual device patterns can indicate fraudulent activity.
Behavioural Analytics
Behavioural analytics monitor how customers interact with your payment system, including typing patterns, mouse movements, and navigation behaviour. Significant deviations from established patterns can trigger additional verification steps.
Real-Time Transaction Monitoring
Advanced monitoring systems analyse transactions as they occur, checking against known fraud patterns, blacklists, and risk rules. Suspicious transactions can be automatically declined or flagged for manual review.
Geolocation and IP Analysis
Analysing the geographic location of transactions and comparing them to customer profiles helps identify potentially fraudulent activity. Transactions from high-risk countries or locations inconsistent with customer behaviour patterns warrant additional scrutiny.
Secure Payment Gateway Protocols and Standards
Payment gateway security elements include encryption, tokenization and fraud prevention to safeguard transactions and sensitive data. Understanding these protocols helps you make informed decisions about your payment infrastructure.
1. PCI DSS (Payment Card Industry Data Security Standard)
PCI DSS is a set of rules for securing cardholder data. It benefits your business by reducing fraud risks, data breaches and potential fines.
You can follow these steps to ensure that your business is PCI DSS compliant:
Assess Data
Regularly evaluate sensitive customer payment data to identify where it’s stored, processed or transmitted within your organisation.
Limit Storage
Minimise the retention of cardholder data to the bare minimum necessary for business purposes. Reducing data storage limits the potential for data breaches and ensures you’re not storing sensitive information longer than required.
Secure Networks
Implement strong network security measures, like firewalls and encryption, to protect payment data during transmission. This prevents unauthorized access or interception of sensitive information while it’s in transit.
Control Access
Restrict access to cardholder data to authorised personnel only. Implement strict user authentication and access controls to ensure that sensitive information is only available to those who need it.
Monitor Data
Continuously monitor data and track potential breaches to detect and respond to threats in real-time.
Maintain Policies
Develop and enforce comprehensive security policies and procedures that align with PCI DSS requirements. This ensures that your organisation follows the best practices for safeguarding payment data and maintaining compliance.
The 12 key requirements of PCI DSS
1. Install and Maintain a Firewall Configuration
Build and maintain a secure network by using firewalls to protect cardholder data.
2. Do Not Use Vendor-Supplied Defaults for System Passwords
Change default passwords and settings to prevent unauthorised access.
3. Protect Stored Cardholder Data
Encrypt stored cardholder data and implement access controls.
4. Encrypt Transmission of Cardholder Data
Use secure encryption protocols when transmitting cardholder data across open, public networks.
5. Use and Update Antivirus Software
Employ antivirus software and keep it up-to-date to protect your systems against malware.
6. Develop and Maintain Secure Systems and Applications
Regularly update and patch systems and applications to address vulnerabilities.
7. Restrict Access to Cardholder Data
Limit access to cardholder data to authorised personnel only, based on a need-to-know basis.
8. Assign Unique User IDs
Assign unique user IDs for system access and authentication to enable monitoring and tracking of individual users.
9. Restrict Physical Access
Implement physical security measures to prevent unauthorised physical access to cardholder data.
10. Track and Monitor All Access to Network Resources and Cardholder Data
Implement logging and monitoring systems to detect and respond to security events.
11. Regularly Test Security Systems and Processes
Conduct regular security testing and vulnerability assessments to identify and address weaknesses.
12. Maintain a Security Policy
Establish and maintain a security policy and ensure all personnel are aware of and follow these practices.
PCI DSS compliance levels are determined by the volume of card transactions a business processes annually. There are four compliance levels:
- Level 1: Over 6 million annual transactions
- Level 2: 1 million to 6 million annual transactions
- Level 3: 20,000 to 1 million annual transactions
- Level 4: Less than 20,000 annual transactions
Secure Electronic Transaction (SET)
SET (Secure Electronic Transaction) is a collaborative system and protocol developed by VISA and Mastercard. It encrypts credit card payment data, safeguarding personal information on the card, thwarting fraud, and preventing unauthorised access. SET also prevents merchants from accessing customers’ data. This boosts transaction security and privacy for consumers, thus mitigating the chances of fraud and data breaches.
Encryption Protocols
SSL (Secure Sockets Layer) and TLS (Transport Layer Security) are encryption protocols that are used by payment gateways. These encryption protocols secure data during online transactions. Here’s the process that is followed via these protocols:
- Handshake: Establish a secure connection.
- Encryption: Encrypt data in transit.
- Authentication: Verify server identity.
- Data transfer: Securely exchange payment information.
- Closure: Safely end the connection.
These protocols help ensure confidential and secure payment transactions.
Tokenization
Tokenization is a security method used in payment systems. It replaces sensitive card data with a token – a unique set of characters. This renders the original information useless to hackers. This enhances security by protecting cardholder information from being exposed during transactions.
Authentication and Fraud Prevention:
Payment authentication protocols verify the identity of users and protect against fraud. Common methods include:
- 3D Secure: A system that adds an extra layer of security by requiring a password or one-time code during online transactions.
- Biometrics: It uses unique physical traits (like fingerprints or facial recognition) to confirm the user’s identity.
- Two-Factor Authentication (2FA): It combines two verification methods, like a password and an OTP, for added security.
- Risk-Based Authentication (RBA): It analyses transaction risk factors to determine the level of authentication required.
These methods help ensure secure and trustworthy payment processes, thus reducing the chances of fraud.
For Which Businesses is Payment Security Important?
Payment security is crucial for all kinds of businesses due to the nature of their operations, large volumes of data handling, and the acceptance of mobile payments. Every business that processes payments—regardless of size or industry—faces security risks that could impact their reputation and bottom line.
1. E-commerce
E-commerce businesses handle vast amounts of sensitive customer data online, making robust payment security vital to protect against data breaches and fraud.
2. Brick-and-mortar stores
Even traditional stores accepting card payments must prioritise payment security to safeguard customer information and maintain trust.
3. Hospitality
The hospitality industry manages numerous transactions and guest data, necessitating secure payment systems to prevent cyber threats.
4. Education
Educational institutions handling tuition payments and student information must ensure payment security to protect sensitive data.
5. Recurring payments
Businesses with subscription models rely on secure payments to manage recurring transactions and safeguard subscriber details.
6. Non-profits
Non-profit organisations handling donations require payment security to protect donor information and maintain credibility.
7. B2B businesses
B2B companies dealing with large transactions should prioritise secure payment gateways to protect the financial data of their clients.
8. Start-ups
Start-ups, often targeted by cybercriminals due to potentially weaker security infrastructure, need strong payment security from day one to establish trust in a new market and protect customer information.
Payment Security Strategy and Best Practices
Building a robust payment security strategy involves several key steps that work together to create a comprehensive defence system for your business.
Conduct a Risk Assessment
Start by identifying vulnerabilities and areas for improvement in your infrastructure, processes and systems. Determine the types of sensitive data you handle, as well as where it’s stored, processed and transmitted.
Document Payment Compliance Requirements
Understand industry regulations like PCI DSS and outline specific compliance needs. Employ security controls and practices mandated by these standards.
Develop and Implement Security Policies
Create clear policies addressing payment security, data handling, access controls, incident response, and staff training. Ensure that these policies align with industry regulations.
Establish Security Measures
Implement security measures like encryption, tokenization, strong authentication and robust firewall configurations. Choose secure payment gateways that adhere to PCI DSS.
Firewall and Network Security
Implement robust firewall configurations and network segmentation to protect payment data. Use intrusion detection systems to monitor for suspicious activity and ensure your network infrastructure meets PCI DSS requirements for secure payment processing.
Security Updates and Patch Management
Establish a systematic approach to keeping all payment-related systems updated with the latest security patches. Create a schedule for regular updates and maintain an inventory of all systems that process payment data to ensure nothing is overlooked.
Monitor Systems and Keep Iterating
Continuously monitor payment systems, networks, and applications for threats and vulnerabilities. Conduct vulnerability scans, penetration tests, and audits to assess effectiveness and adapt to evolving threats. Keep evaluating the effectiveness of your security strategies to meet the changing needs of your business and industry regulations.
Develop an Emergency Response Plan
Craft a well-defined incident response plan, delineating roles, communication protocols and procedures for containing and mitigating security breaches. Adapt and protect your customers’ data.
Conduct Regular Employee Training
Continuously educate your staff on payment security practices to reduce human errors that could compromise security. Regular training helps your team recognise and respond to emerging threats.
Encrypt Data
Implement robust encryption for data at rest and in transit to safeguard sensitive information from unauthorised access.
Key takeaways
- Start with a comprehensive risk assessment to identify your specific vulnerabilities
- Implement multiple layers of security rather than relying on a single solution
- Regular employee training is as important as technical security measures
- Continuous monitoring and updates are essential—security isn’t a one-time setup
- Have an incident response plan ready before you need it
Why Payment Security Matters for Businesses
Payment security isn’t just a technical requirement—it’s a fundamental pillar of trust in today’s digital economy. Understanding why it matters helps you prioritise the right investments and strategies for your business.
- Protecting customer data: Your payment systems ensure that customers’ sensitive financial information, such as credit card numbers and personal details, remains confidential. Any breach in this security could expose customers to identity theft and financial loss.
- Safeguarding business reputation: Security breaches can inflict substantial damage to a company’s reputation. News of a data breach spreads quickly, eroding customer trust and confidence. Businesses may struggle to recover the lost trust, often facing long-term consequences.
- Avoiding legal and financial consequences: Security breaches can lead to severe penalties and fines. For instance, GDPR violations can result in hefty penalties, and non-compliance with PCI DSS may lead to fines or even the loss of the ability to process card payments.
- Enhancing customer experience: In the realm of e-commerce, secure payment processing is pivotal. Customers need assurance that their transactions are safe. Providing a secure shopping environment not only keeps customers loyal but also encourages repeat business.
How Razorpay Simplifies Payment Security
Razorpay understands that payment security shouldn’t be a burden on your business operations. The platform combines industry-leading security measures with user-friendly implementation, allowing you to focus on growth whilst maintaining the highest security standards.
Best-in-Class Security Features
- PCI DSS Level 1 Compliance: The highest level of payment security certification
- Advanced Fraud Detection: Real-time monitoring with machine learning algorithms
- End-to-End Encryption: Your customer data is protected at every step
- Tokenisation: Sensitive card data is replaced with secure tokens
- 3D Secure Authentication: Additional layer of verification for card transactions
Comprehensive Protection for Indian Businesses
Razorpay’s security infrastructure is specifically designed for the Indian market, understanding local payment preferences and regulatory requirements. The platform processes over 10 billion transactions annually, with a track record of maintaining the highest security standards.
Key differentiators include:
- 24/7 Security Monitoring: Round-the-clock surveillance of all payment activities
- Automated Risk Management: Intelligent systems that adapt to your business patterns
- Regulatory Compliance: Automatic updates to meet evolving Indian payment regulations
- Dedicated Support: Expert security team available for consultation and incident response
Secure Your Payments with Razorpay →
Common Payment Security Threats and How to Prevent Them
While payment gateways do their best to ensure data security, fraudsters work equally hard to exploit vulnerabilities. Staying aware of common attack methods helps you implement the right preventive measures.
| Type of Threat | How it Works | Prevention Strategies |
|---|---|---|
| Phishing or Spoofing | Accessing personal information through fraudulent emails or websites that appear legitimate | Implement email authentication, educate customers about suspicious communications, and use multi-factor authentication |
| Data Theft | Card details and sensitive data stolen through insider threats or system vulnerabilities | Use encryption, implement strict access controls, conduct background checks, and maintain audit trails |
| Fake Schemes and Offers | Fraudulent offers that provide unrealistic discounts to steal payment information | Verify merchant authenticity, use secure payment methods, and implement transaction monitoring |
You should always use two-factor authentication to make online payments. It adds an extra layer of security to digital transactions.
For example, even if your data gets compromised and someone gains access to your card details, they won’t be able to complete a transaction without the OTP that comes to your phone number when you have two-factor authentication enabled.
Ready to streamline your payments?
Scale your business with a gateway that supports 100+ payment methods, including UPI, Credit Cards, and Netbanking. Transition to a reliable infrastructure designed to improve transaction success rates and automate your daily reconciliation.
Conclusion
Payment security isn’t just an operational detail—it’s the foundation that enables your business to thrive in the digital economy. By implementing comprehensive security measures, staying compliant with industry standards, and choosing the right payment partners, you’re not just protecting transactions—you’re building lasting customer trust.
Remember, effective payment security combines multiple layers of protection: from encryption and tokenisation to fraud detection and employee training. The key is to start with a solid foundation and continuously adapt to emerging threats.
By making security a top priority, businesses can not only thrive but also build enduring relationships with their customers, fostering a climate of trust and confidence in an increasingly interconnected world.
Ready to Secure Your Payments?
Protect your business and customers with Razorpay’s PCI DSS Level 1 certified payment solutions. Join over 10,000+ Indian businesses that trust Razorpay for secure, seamless payments.
Frequently Asked Questions
What do you mean by payment security?
Payment security refers to the comprehensive measures and protocols you implement to protect sensitive financial information during transactions. It includes encryption, authentication, fraud detection, and compliance with industry standards like PCI DSS to safeguard both your business and customers from financial threats.
What are the four types of security in payment systems?
The four main types of payment security are: 1) Network security (firewalls, secure connections), 2) Data security (encryption, tokenisation), 3) Application security (secure coding, regular updates), and 4) Physical security (secure terminals, restricted access). Each type works together to create comprehensive protection for your payment infrastructure.
How can businesses ensure secure online payments?
You can ensure secure online payments by implementing PCI DSS compliance, using encrypted payment gateways, enabling multi-factor authentication, conducting regular security audits, training your staff on security best practices, and partnering with reputable payment processors that offer advanced fraud detection capabilities.
How do payment gateways encrypt payment information?
Payment gateways encrypt payment information using secure protocols like SSL and TLS, converting data into unreadable code during transmission.
What is tokenization in payment gateway security?
Tokenization replaces sensitive data with unique tokens, rendering the data unreadable even if intercepted by unauthorised individuals.
What is two-factor authentication and how does it enhance payment gateway security?
Two-factor authentication requires you to provide two forms of verification, typically something you know (e.g., password) and something you receive (e.g., a one-time code), thus significantly enhancing security.
What are some common fraud detection techniques used by payment gateways?
Payment gateways employ common fraud detection techniques such as IP geolocation, velocity checks, and machine learning algorithms to identify suspicious transactions.
How can businesses ensure that their payment gateway is secure?
You can ensure payment gateway security by selecting reputable providers with robust security measures, regularly updating software, and complying with industry standards like PCI DSS.