The internet has revolutionised the way businesses collect customer payments. However, fraud vulnerabilities and security breaches make internet security a challenging task. As a business owner, you must strive to deliver an excellent payment experience to your customers when they make payments through different online payment channels. This can be achieved by having sufficient security measures in place.
Businesses must be extra cautious about cyber threats while collecting online payments from customers as payment frauds involving credit cards and digital wallets made up 92% of all customer frauds reported in India in 2022. You must have various online payment security measures in place to protect customer data and to provide them with a safe experience.
Table of Contents
What is Online Payment Security?
Online payment security refers to the measures used to protect financial transactions, customer funds, and personal data from risks like fraud, unauthorized access, and data breaches.
If a customer’s money or information is compromised, your business could face serious legal and financial consequences. To avoid this, it’s essential to have a secure payment system in place that safeguards transactions and builds customer trust.
11 Best Practices for Secure Online Payment Processing
1. Data Encryption (TLS & SSL Protocols)
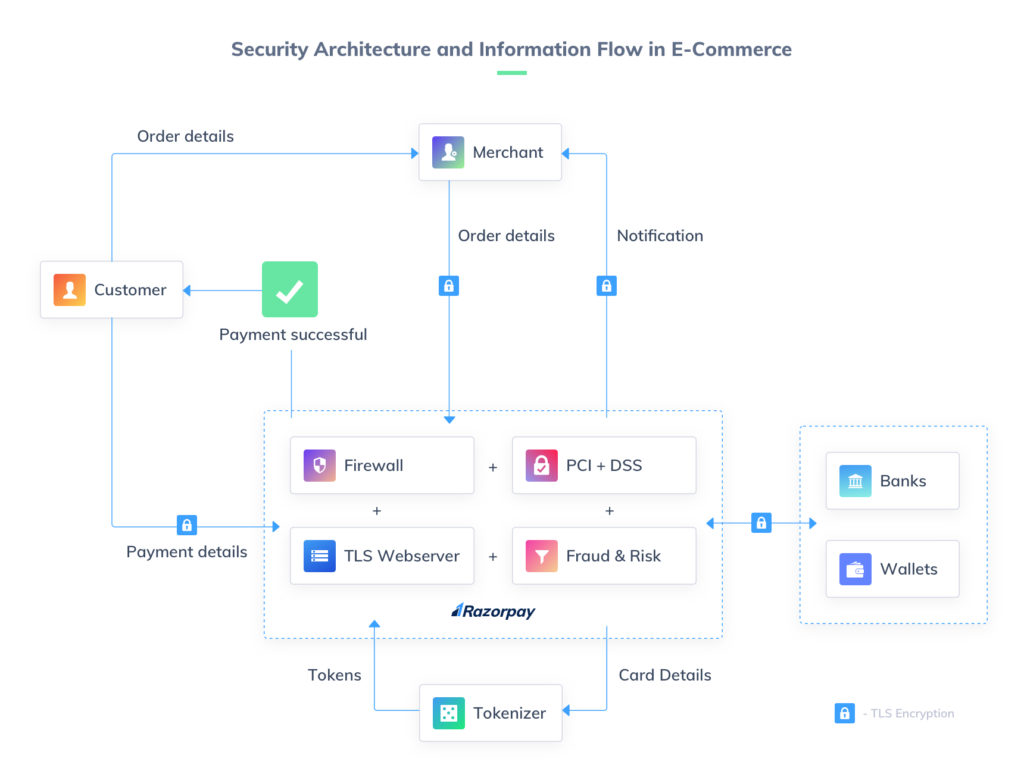
Data encryption is the process of encoding the payment information so that only the person who holds the encryption key can decode it. The data is encrypted to provide end-to-end protection.
TLS (Transport Layer Security) and SSL (Secure Sockets Layer) are two key protocols that are used to encrypt data.
SSL is an internet security protocol based on encryption. It was developed in 1995 to guarantee data integrity, privacy and authenticity in online communications.
TLS is a cryptographic security protocol that emerged from SSL and is used to preserve data integrity and anonymity for communications over the Internet. Its most widely-known use is for securing HTTPS. Without TLS encryption in place, all data sent over the Internet is unencrypted and is visible to anyone with the means and intent to intercept it.
An easy way to check if the e-commerce websites you frequent are SSL-certified is to look at the URL and see if they use the “http://” or the “https://” protocol. The additional ‘s’ signifies a secure e-payment system. You can also look for the padlock icon at the beginning of the URL. Modern web browsers, in their race to make the Web secure by default, are marking HTTP sites as ‘insecure’.
The more recent protocol, TLS, can be considered an upgrade to SSL. Compared to SSL, TLS is easier to use, more dependable, and offers more security. SSL is less prevalent than TLS.
2. PCI-DSS Compliance
The PCI Security Standards Council is a global organisation that maintains and promotes compliance rules for managing cardholder data for all e-commerce websites and online payment systems.
The Payment Card Industry Data Security Standards (PCI-DSS) is, in effect, a set of policies that govern how sensitive cardholder information should be handled.
Fact: The PCI Security Standards Council was created as a joint initiative by the four major credit-card providers: American Express, Visa, MasterCard, and Discover, in the year 2004. Over the years, the PCI-DSS standard has become the guiding principle for online security across the globe.
For an e-commerce website or an online payment system to be PCI-DSS compliant, they have to follow certain directives:
Maintain a secure network to process payments
- Use robust firewalls to safeguard your website from malicious security threats.
- Make sure your payment gateway or website does not use default credentials, like PINs or passwords provided by the manufacturer.
- Allow customers to change their credentials whenever necessary on your website or payment gateway.
Ensure all data is encrypted during transmission
The cardholder data should be encrypted before it is transferred online. Razorpay encrypts all information you share using checkout via TLS. This prevents data interception during transmission from your system to Razorpay.
Keep infrastructure secure
This directive involves –
- Staying aware of new PCI-DSS mandates.
- Using updated software and spyware to protect against known software vulnerabilities.
- Running regular system and software scans to provide maximum data protection.
Restrict information access
Cardholder data must be protected at all times, both electronically and physically.
e-Commerce websites must restrict access to confidential information so that only authorised personnel can access cardholder data.
3. 3D Secure
3D Secure is used to maintain payment security in e-commerce by verifying a customer’s identity. It serves as an extra layer of authentication during the online checkout process and is administered by the cardholder’s bank.
3D Secure is implemented to prevent the unauthorised use of cards. It can include biometric scans or entering PIN codes to verify the cardholder’s identity.
The many advantages of 3D Secure are as follows –
- Reduced risk of online payment fraud
- Enhanced protection of customer data
- Increased customer confidence
4. Choose the Right Platform and Payment Gateway
Choosing the right platform and payment gateway is extremely crucial for maintaining online payment security. The security of your payment gateway should be your top concern when accepting payments online as you’re handling the sensitive financial data of your customers. You should ascertain that the payment getaway and platform chosen by you is well-known in the industry and has clearly outlined what security measures it uses.
Your business can save significant money and reputation by investing in a safe platform and payment gateway right from the start. With the global annual cost of cybercrime having surpassed USD 10.5 trillion recently, the stakes have never been higher. The key takeaway? Cyber threats lead to grave consequences, and partnering with a heavily encrypted, future-proof payment system is non-negotiable for e-commerce success.
5. Updated Operating Systems
You must keep your operating systems updated to be certain that your system has the most recent security measures.
Keeping your operating systems updated is an important part of reducing the threat of data breaches caused by hackers and fraudsters, as well as minimising vulnerabilities in the system. The focus should be on being proactive instead of reactive and trying to reduce the chances of cybercrime beforehand.
6. Payment Tokenization
Tokenization is a process by which a 16-digit card number gets replaced by a digital identifier known as a ‘token’. This is done for the safety of the original data while allowing payment gateways to securely access the cardholder data and initiate a secure payment.
Fact: Even if a website gets breached and the tokens stored are hacked, it is immensely difficult to reverse-engineer the actual card number from the token itself. To do this, one needs access to the logic used for tokenization, which is not publicly available.
Credit card tokenisation helps e-commerce websites improve security, as it eliminates the need for storing credit card data, and reduces security breaches. For more on how tokenization works and impacts online payments, you can read our in-depth blog.
7. Two-Factor Authentication
Two-factor authentication (aka 2FA, or two-step verification) is a security method that uses two different methods to authenticate the identity of the user before granting access to a website.
Fact: 2FA has evolved far beyond simple SMS OTPs. Today, leading digital platforms and payment gateways integrate advanced, frictionless authentication methods—like biometric fingerprint scans, facial recognition, and authenticator apps—to provide ironclad security without slowing down the customer checkout experience..
When you use NetBanking for a transaction, you are first asked to enter your username and password. As a final confirmation, the bank sends you an OTP on your registered mobile number. This process has been mandated by the RBI and is divided into two levels of authentication:
What the user knows
In this first step, users fill in their card / NetBanking details such as username and password. This helps the payment gateway recognize which bank the card belongs to.
What the user (and only the user) has
This step is known as ‘authorization’ and is done via OTP / PIN / CVV. The bank (and the payment gateway) can then confirm that the payment request is initiated by the rightful user.
Two-factor authentication is an extra layer of security added by e-commerce websites to provide a secure payment experience for a customer. It is a customer-facing authentication process, where the transaction is processed only after the user enters a detail that only they could know, or have at hand (like a physical token or a security key). Many banks and e-payment gateways use 2FA for their payment modes.
8. Verify Transaction Details
Online financial transactions are risky because they could be completed without actually holding a physical card. Businesses can reduce the risk of unauthorised payments by verifying the details of users, such as CVV, billing address, phone number, and email ID.
9. Fraud Prevention and Monitoring Systems
Apart from the mandatory protocols mentioned above, most e-commerce websites and payment gateways have their own fraud and risk prevention systems. Big data analytics and machine learning play a huge role in devising these risk prevention and mitigation systems.
By delving into our customer’s data and analysing patterns, we at Razorpay can discern between a ‘normal’ and a ‘suspicious’ transaction with credible accuracy. Apart from this, there is a lot that you as a customer can do to reduce the risk of fraud.
10. Train Employees in Security Measures
Take steps to make sure that your team understands what is online payment security. Your employees should be able to recognise potential threats and take the appropriate action. Set up seminars and training sessions to thoroughly educate your staff on data protection guidelines, multiple security measures and protocols, and other related topics.
11. Explain Security Measures to Customers
Once the security measures are in place, it is crucial to let your customers know about them so that they feel secure when making transactions on your website. Make an effort to promote the data protection procedures you have put in place.
For instance, inform your clients that two-factor authentication is used by your company to thwart fraudulent online purchases. Mention that your company employs a reliable payment gateway that complies with PCI standards.
How AI and Machine Learning are Revolutionizing Payment Security
Traditional, rule-based security measures are no longer enough to combat sophisticated, modern cyber threats. Today, Artificial Intelligence (AI) and Machine Learning (ML) are actively shifting e-commerce security from a reactive approach to a predictive one.
Here is how AI is changing the game for online businesses:
-
Real-Time Threat Detection: Machine learning algorithms can analyze millions of data points—such as a user’s IP address, typing speed, device type, and purchasing habits—in mere milliseconds. If a transaction deviates from a customer’s normal behavior, the AI flags or blocks it before the checkout is even completed.
-
Reducing False Positives: One of the biggest challenges for merchants is “false declines” (accidentally blocking a legitimate customer due to strict security rules). AI risk engines learn over time, easily distinguishing between a genuine buyer making an unusual purchase and a real fraudster. This protects your revenue and prevents customer frustration.
-
Dynamic Authentication: Instead of forcing every customer through a rigid 2FA process, AI enables “risk-based authentication.” Low-risk transactions sail through a frictionless checkout, while only high-risk transactions are challenged with an OTP or biometric prompt.
Which Businesses Should Prioritize Payment Security?
Any business that processes, stores, or transmits payment information, including credit card data, must prioritize payment security. No matter the size, industry, or business type, securing payment processes is crucial for protecting customer data, maintaining trust, and complying with industry regulations.
Here are some common types of businesses that need to ensure payment security:
1. E-commerce Businesses:
Online stores and service providers accepting payments via websites or mobile apps must use secure payment gateways, encryption, and other safeguards to protect customer data.
2. Retail Shops:
Physical stores using point-of-sale (POS) systems need to secure their payment terminals, networks, and stored customer data to prevent fraud.
3. Hospitality Businesses:
Hotels, restaurants, and other hospitality businesses should implement secure POS systems, tokenization, and access controls to safeguard guest payment details.
4. Businesses that Accept Recurring Payments:
Companies offering utilities, telecom, or subscription services must secure recurring payment processes and stored financial data.
5. Non-Profit Organisations:
Charities and nonprofits handling donations, event payments, or memberships should ensure secure payment methods to protect donor information.
6. B2B Businesses:
Businesses handling transactions with suppliers, vendors, or partners must maintain strong payment security to protect financial data and build trust.
How to Build a Strong Payment Security Strategy?
Payment security is a complex challenge, but with the right approach, businesses can create a secure environment that builds customer trust and ensures compliance. Here’s how:
1. Assess Risks:
Analyze your payment infrastructure to spot vulnerabilities and identify where sensitive data is stored, processed, and transmitted.
2. Understand Compliance:
Stay informed about industry regulations like PCI DSS and ensure your security practices meet compliance standards.
3. Set Clear Policies:
Define security policies for handling sensitive data, access controls, incident response, and employee training.
4. Implement Security Measures:
Use encryption, tokenization, strong authentication, and firewalls. Work with PCI DSS-compliant vendors for secure payment processing.
5. Monitor and Test Systems:
Regularly scan for vulnerabilities, conduct penetration tests, and audit security measures to identify and fix weaknesses.
6. Adapt as Needed:
Continuously review and update your security strategy to address new threats, business changes, or regulatory updates.
7. Prepare for Incidents:
Have a clear incident response plan that outlines roles, communication steps, and mitigation strategies in case of a breach.
Things to Remember Before Making an Online Payment
- Anyone of importance will never ask for your card data/passwords up front. Banks and financial service providers have a safe protocol to gain admin access to an account if the need ever arises.
- Passwords are safer when you don’t write them down. Keep strong passwords that you can remember, change them frequently, and refrain from writing them down somewhere.
- You have the right to dispute suspicious charges on your card or accounts. Raise a chargeback request for any unidentified transaction on your card. You have a legal right to a resolution.
Conclusion
Ensuring online payment security has become crucial for running a successful digital business. One little crack in the security system can provide criminals access to client information and enable them to perpetrate financial fraud. The customer might sustain significant financial losses, and your company might experience serious legal repercussions, including fines and a damaged reputation.
We are fortunate to have access to cutting-edge security techniques that let you accept consumer payments online securely without endangering your customers’ personal information. Follow all possible online payment security methods in your company to provide customers with a safe and reliable experience.
Frequently asked questions
What should you do to ensure secure online transactions?
For secure online transactions, use a secured internet connection, keep your software up-to-date, use strong passwords that you can remember without writing down, check website security before paying, and do not share passwords and card information with anyone.
What is the most secure online payment method?
Paying via a credit card is considered to be the most secure online payment method.
What is a security issue in online banking?
Cyber fraud is a major security issue in online banking. This includes threats of phishing scams, identity theft, malware attacks, etc.
What should I do if my payment details are stolen?
Immediately report it to your bank, freeze your card, update passwords, and monitor transactions for fraud.
Can online payment security prevent chargebacks?
It reduces fraud-related chargebacks but can’t prevent all disputes, like customer dissatisfaction or delivery issues.